by Sol Nasisi
Share
by Sol Nasisi

How to Verify a College Degree or Digital Credential
Verifying a college degree sounds simple — until you actually have to do it. An applicant submits a diploma or transcript. It looks legitimate. The formatting is clean. The institution is recognizable. But one question remains: Is it real?
For decades, verification relied on trust, manual processes, and institutional authority. That model is now under serious strain. AI tools can generate convincing fake credentials in minutes, and many digital verification systems depend on links or platforms that are one vendor decision away from going dark.
This guide covers how degree verification actually works today, where each method breaks down, and what genuinely reliable verification needs to look like going forward.
Why Degree Verification Matters More Than Ever
Degree verification isn’t just an administrative checkbox — it’s a trust mechanism that serves two sets of stakeholders with very different concerns.
Employers rely on it to confirm that candidates hold the qualifications they claim, reduce hiring risk, and satisfy compliance requirements in regulated industries. A bad hire based on a fraudulent credential isn’t just costly — in healthcare, finance, or law, it can carry legal liability.
Institutions rely on it to protect the value of the degrees they issue. Every fraudulent diploma in circulation dilutes the credential’s meaning. Institutions also have a practical interest in reducing the manual workload that traditional verification creates for registrar offices.
The problem is that the environment has changed faster than most verification systems have adapted.
The AI credential threat is real. Today, someone with basic design skills can recreate a diploma layout in minutes, modify a PDF transcript without leaving visible traces, or use AI tools to generate entirely fabricated credentials that pass a visual inspection. Visual authenticity no longer equals real authenticity.
How Degree Verification Works Today
There are three methods most organizations rely on to verify academic credentials. Each has meaningful limitations.
1. Direct Registrar Verification
This is the oldest and most trusted approach. An employer contacts the institution directly, and the registrar’s office manually confirms whether the applicant’s record exists and matches what was claimed.
It’s highly trusted precisely because it goes to the source — but that source comes with real costs. The process typically takes days or weeks, it requires back-and-forth communication that doesn’t scale, and for high-volume hiring, it creates a serious bottleneck. It also places an ongoing operational burden on registrar offices that are already stretched thin.
2. Third-Party Verification Services
Organizations like the National Student Clearinghouse act as intermediaries, maintaining aggregated records that employers can query through a platform rather than contacting each institution individually. This is faster and more standardized than direct registrar contact.
But it introduces a different set of dependencies. These services require accounts, carry fees, and — critically — rely on centralized infrastructure. If the vendor has an outage, changes its data access model, or discontinues a service, the verification chain breaks. The credential itself hasn’t changed, but the ability to verify it has.
3. Digital Diplomas with Verification Links
Many institutions now issue digital diplomas or certificates that include a URL — the recipient shares the link, and the verifier visits a hosted page confirming authenticity. This is faster and easier to distribute than anything that came before it.
The vulnerability, however, is structural. The verification link is only as reliable as the system hosting it. If the vendor changes platforms, the institution switches providers, or the hosting environment goes offline, the link breaks. A 404 error where a verification page should be doesn’t tell the verifier the credential is fake — but it creates exactly the kind of doubt that erodes trust.
The Core Problem: Verification Depends on Systems That Can Fail
Looking across all three methods, a common structural flaw emerges: they all require an external system to be available, operational, and trustworthy at the moment verification is needed.
That creates a predictable set of failure modes. What happens if the vendor shuts down? What if the URL changes after a platform migration? What if the database becomes unavailable during an audit? In each case, the credential becomes difficult — or impossible — to verify, through no fault of the issuing institution or the credential holder.
This is the verification dependency problem: the credential and its proof of authenticity are stored in separate places, and the proof can disappear even when the credential is genuine.
For credentials that need to remain verifiable for years or decades — academic degrees, professional certifications, compliance completions — this is a serious architectural weakness.
Modern Approaches
The Shift Toward Independent Verification
Two newer approaches move verification away from centralized system dependency — with meaningfully different results.
Database-Based Verification
A credential ID is checked against a hosted database. Faster than manual registrar contact and more scalable — but verification still depends entirely on platform availability, data integrity, and vendor continuity. The credential and its proof live in different places.
⚠ Still system-dependent
Cryptographic File-Based Verification
Verification is embedded directly into the credential file itself via a unique cryptographic fingerprint. Any modification to the file invalidates the fingerprint. Verification can occur independently of any central system — no login, no vendor dependency, no broken links.
✓ System-independent
The Core Shift
From “ask the system if this credential is real” — to “verify the credential directly, without asking anyone.”
The Standard
What Makes a Credential Truly Verifiable?
A credential that can’t be verified under adverse conditions offers only conditional trust. Reliable verification needs to meet five criteria — unconditionally.
No waiting, no manual intervention, no phone calls to a registrar office. Verification should return a result in seconds.
Verification must be accessible to anyone — an employer, a licensing board, a background check vendor — without a subscription or login.
Any modification to the credential — a name, a date, a single character — should immediately invalidate it. Tamper detection must be automatic, not reliant on visual inspection.
Verification must not rely on a single vendor, platform, or database remaining operational. If the issuing platform disappears tomorrow, every credential it issued should still be verifiable.
A degree earned in 2005 should be as verifiable in 2045 as it was the day it was issued. Credentials that age out of verifiability undermine the entire point of issuing them.
A Real-World Failure Scenario
Consider a scenario that plays out more often than most institutions realize.
A graduate applies for a position five years after completing their degree. The hiring manager requests verification. The graduate shares the digital diploma they received at graduation — a nicely formatted PDF with a verification link embedded in it. The hiring manager clicks the link.
The page returns a 404 error. The institution migrated to a new student records platform two years ago. The old verification URLs were never redirected.
Now the hiring manager has a problem. The credential exists and is genuine — but it can’t be verified through the channel it was designed for. The options are to assume the credential is invalid, contact the institution directly and wait days for a response, or proceed without verification and accept the risk.
In each case, trust is damaged — not because the graduate did anything wrong, but because the verification system failed to outlast the platform that hosted it.
This scenario isn’t hypothetical. Institutions routinely change platforms, consolidate systems, or sunset legacy infrastructure. Every time they do, previously issued credentials become harder to verify. And the credential holder — who earned that degree legitimately — bears the consequences.
How Employers Actually Handle Credential Verification
In practice, most employers don’t have a systematic verification process. Many skip verification entirely unless the role requires it by regulation. Others rely on background check vendors who operate their own aggregated databases — with the same dependency risks described above. Many use inconsistent processes that vary by hiring manager or department.
This creates a gap between what institutions assume is happening when they issue a credential and what employers actually do when they receive one. Institutions invest in digital issuance platforms expecting that verification will follow. Employers, facing friction in the verification process, frequently don’t follow through.
The result is a credentialing ecosystem built on assumed trust rather than verified trust — which is precisely the environment in which credential fraud thrives.
The Direction Forward
The trajectory is clear. As AI continues to make visual forgery easier, and as credential fraud becomes more sophisticated, organizations will need to move toward verification methods that don’t require visual inspection or centralized system availability.
The most durable approach treats verification as a property of the credential itself — not something that requires checking in with an external authority. A cryptographic fingerprint embedded in the credential file, anchored to an immutable public record, can be verified by anyone at any time without depending on the issuing platform’s continued existence.
That’s the direction the credentialing industry is heading. Institutions and organizations that adopt this model now aren’t just solving a current problem — they’re building a verification infrastructure that will still work reliably in twenty years.
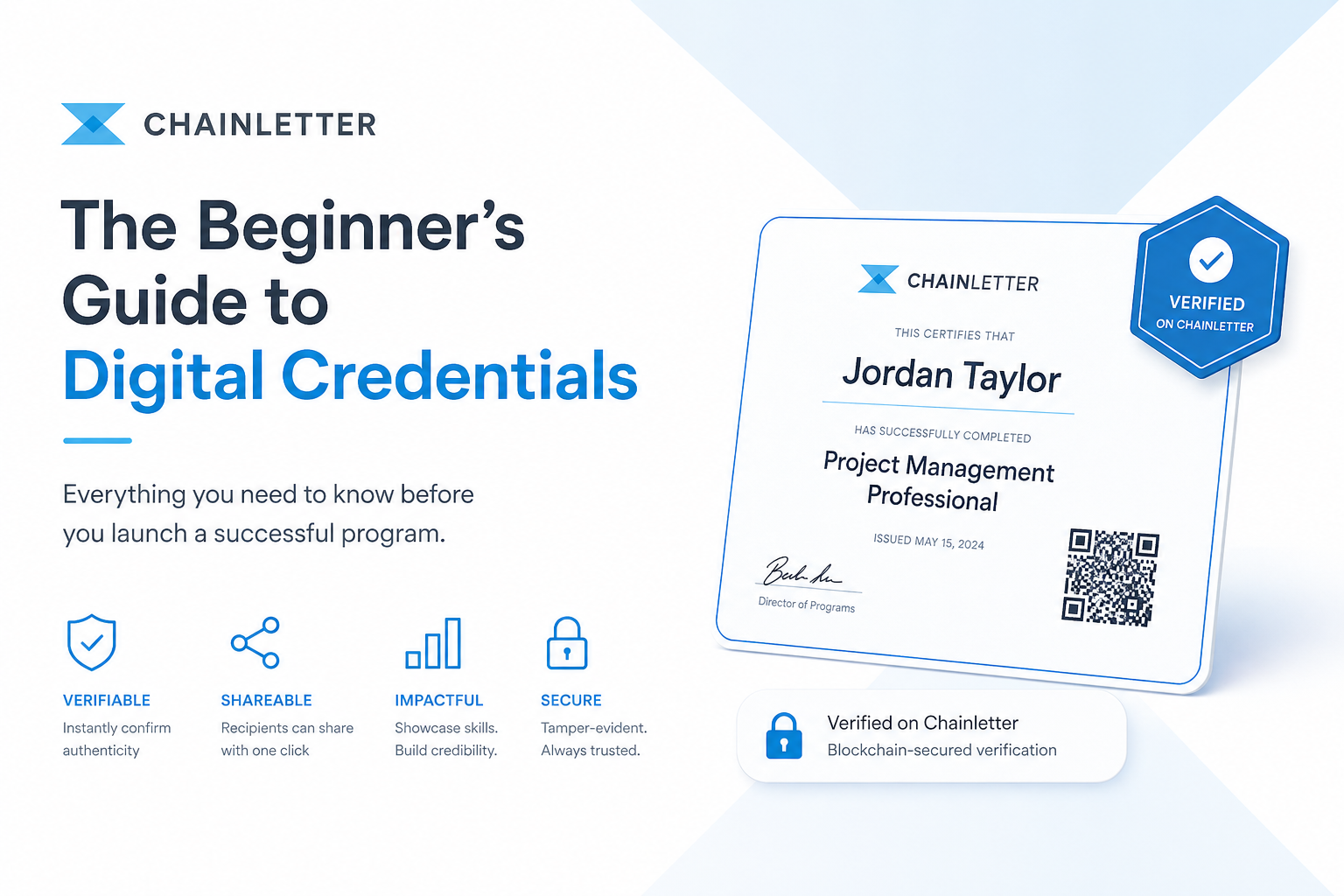
How Chainletter Approaches This Problem
Chainletter was built around a simple premise: verification should be a permanent property of the credential — not a service that can go offline.
Every credential issued through Chainletter receives a cryptographic fingerprint that is anchored to a public blockchain. The verification record exists independently of Chainletter’s platform. If Chainletter’s servers went dark tomorrow, every credential it ever issued would still be fully verifiable — because the proof isn’t stored on Chainletter’s servers. It’s stored on a decentralized public ledger that no single party controls.
That’s not a feature. It’s a foundational architectural choice that addresses the verification dependency problem at its root.
For institutions issuing academic credentials, professional certifications, or compliance completions that need to remain verifiable for years or decades, that architecture matters. Learn more about how Chainletter works at chainletterlabs.com.
Build for the Long Term
Issue Credentials That Verify Themselves
Chainletter issues blockchain-anchored credentials that are verifiable by anyone, at any time, without depending on a central system. No broken links. No vendor lock-in. No expiration date on trust.