by Sol Nasisi
Share
by Sol Nasisi

Fake Digital Invitations Are a Phishing Trap. Here’s Why They Work.
You get an invitation to a birthday party from someone you know. The design looks right. The details feel personal. So you click—before you think, because it feels familiar. That moment is exactly what attackers are exploiting, and fake digital invitations have become one of the fastest-growing phishing vectors targeting everyday users.
A recent report from The New York Times highlighted the growing tactic: scammers are sending fraudulent event invitations that convincingly mimic legitimate platforms like Evite and Paperless Post. These are not the sloppy, misspelled scam emails most people have learned to spot. They are well-designed, emotionally targeted, and increasingly personalized — sometimes referencing real relationships, sometimes mirroring the exact tone and structure of a genuine invitation from a trusted sender.
They work because invitations are built on trust. When you receive one, your instinct is to engage, not interrogate. And attackers know it.
Why Phishing via Digital Invitations Is Harder to Detect
Most phishing guidance focuses on email: check the sender address, look for spelling errors, hover over links before clicking. Those heuristics don’t translate well to event invitations, which arrive through platforms, are forwarded by real people, and are designed to prompt immediate action. The emotional context — a birthday, a wedding, a work event — creates urgency that bypasses the skepticism most users apply to cold emails.
The deeper issue is that digital invitations, like most digital documents, have no native mechanism for proving authenticity. When you receive a file or a link, there is no built-in way to answer the most basic questions: Did this actually come from the sender it claims? Has the content been altered in transit? Is this the original version, or a manipulated copy? In the absence of that verification layer, users fall back on appearance — and appearance is now trivial to fake.
Phishing is the symptom. The real problem is that digital files have no native way to prove they are what they claim to be. Appearance is not proof.
How Generative AI Has Changed the Scale of the Problem
For years, one reliable signal of a fake invitation or fraudulent document was the effort required to produce it. Crafting a personalized, visually convincing fake took time, skill, and knowledge of the target. That friction is gone.
Generative AI tools can now mimic writing styles and tones accurately, personalize messages at scale across thousands of targets simultaneously, and produce convincing visual designs in seconds. The cognitive shortcuts that served as a reasonable first filter — does this look like it came from someone I know, does the tone feel right, does the design match the platform — are now exploitable signals, not protective ones. Attackers are training on the same visual and stylistic cues that users trust.
The result is a fundamental shift in the threat landscape. You can no longer rely on instinct or visual inspection to spot a fake.
Why Even Legitimate Platforms Can’t Solve This
It’s tempting to assume that the platform itself provides a verification guarantee — that an invitation delivered through Evite or Paperless Post is implicitly authenticated. But platform delivery only tells you the message passed through a particular system. It says nothing about whether the content is what the sender intended, or whether the invitation was intercepted or modified before it reached you.
Consider a related example that illustrates the integrity problem. When you upload an image to LinkedIn, the platform automatically compresses and alters the file. If you download that image and compare it byte-for-byte to the original, the files are no longer identical. That matters, because authentic verification depends on exact integrity. A file that has changed — even imperceptibly — should fail verification. That is not a flaw in the verification model. That is precisely the point.
Platform delivery is not authentication. A file that passes through a system is not the same as a file that has been cryptographically verified as unaltered.
The Shift from Trusting Appearance to Verifying Authenticity
The dominant model for evaluating digital documents today is essentially: “It looks real, so it probably is.” That model made reasonable sense when producing convincing fakes required meaningful effort. It no longer does. The only durable alternative is a shift from trusting appearance to verifying authenticity — moving the question from “does this seem legitimate?” to “can this prove it is legitimate?”
That shift requires verification to happen at the file level, not the platform level. It requires that the proof travel with the document, independent of any database lookup or central authority. And it requires that any modification — no matter how small — render the verification invalid. These are the properties of cryptographic stamping: a file carries its own tamper-evident proof of origin and integrity, and anyone — or any AI system — can verify it without trusting an intermediary.
What a Trustworthy Digital File Should Be Able to Prove
A file that can’t be verified under adverse conditions offers only conditional trust. Five properties distinguish a verifiable document from one that merely looks authentic.
- Confirmed origin. The file can prove it was created by a specific issuer at a specific time — not just that it claims to be.
- Tamper evidence. Any modification to the file — including invisible compression changes — causes verification to fail immediately and definitively.
- Platform independence. Verification does not require contacting the issuing platform or organization. The proof is self-contained in the file.
- Machine-readable. AI systems and automated pipelines can verify the file without human review, so verification scales with the volume of documents.
- Binary result. Verification is not a confidence score or a visual indicator. It passes or it fails. There is no ambiguous middle ground that can be exploited.
What Digital Artifact Types Are at Risk
Event invitations are the most immediate example of this problem, but the verification gap applies to any digital artifact that carries trust as a core function.
Diplomas and academic credentials are frequently forged and submitted to employers and licensing bodies who have no reliable way to verify them without contacting the issuing institution directly. Contracts and legal documents circulate as PDFs with no built-in mechanism to confirm that the version a recipient opens is identical to the version the counterparty signed. Medical records, identity documents, and professional certifications all share the same structural weakness: the file’s appearance is treated as its proof.
The question is the same across all of these — not “does this look authentic?” but “can this prove it has not been altered since the moment it was created?” That is a question that appearance alone cannot answer, and that no amount of user education will make answerable through visual inspection.
How to Test File Integrity Yourself
If you want to understand the practical difference between appearance and cryptographic proof, the test is straightforward. Start with a file that has been cryptographically stamped at the time of creation — meaning a hash of its contents has been anchored to an immutable record. Run that file through a verification tool. It passes.
Now open the file, change a single character — a space, a punctuation mark, anything — and save it. Run it through the verification tool again. It fails. The file looks nearly identical. Its contents are functionally unchanged. But the verification is definitive: this is not the same file.
That gap — between what looks the same and what is the same — is where phishing lives. And it is a gap that no amount of visual sophistication can close.
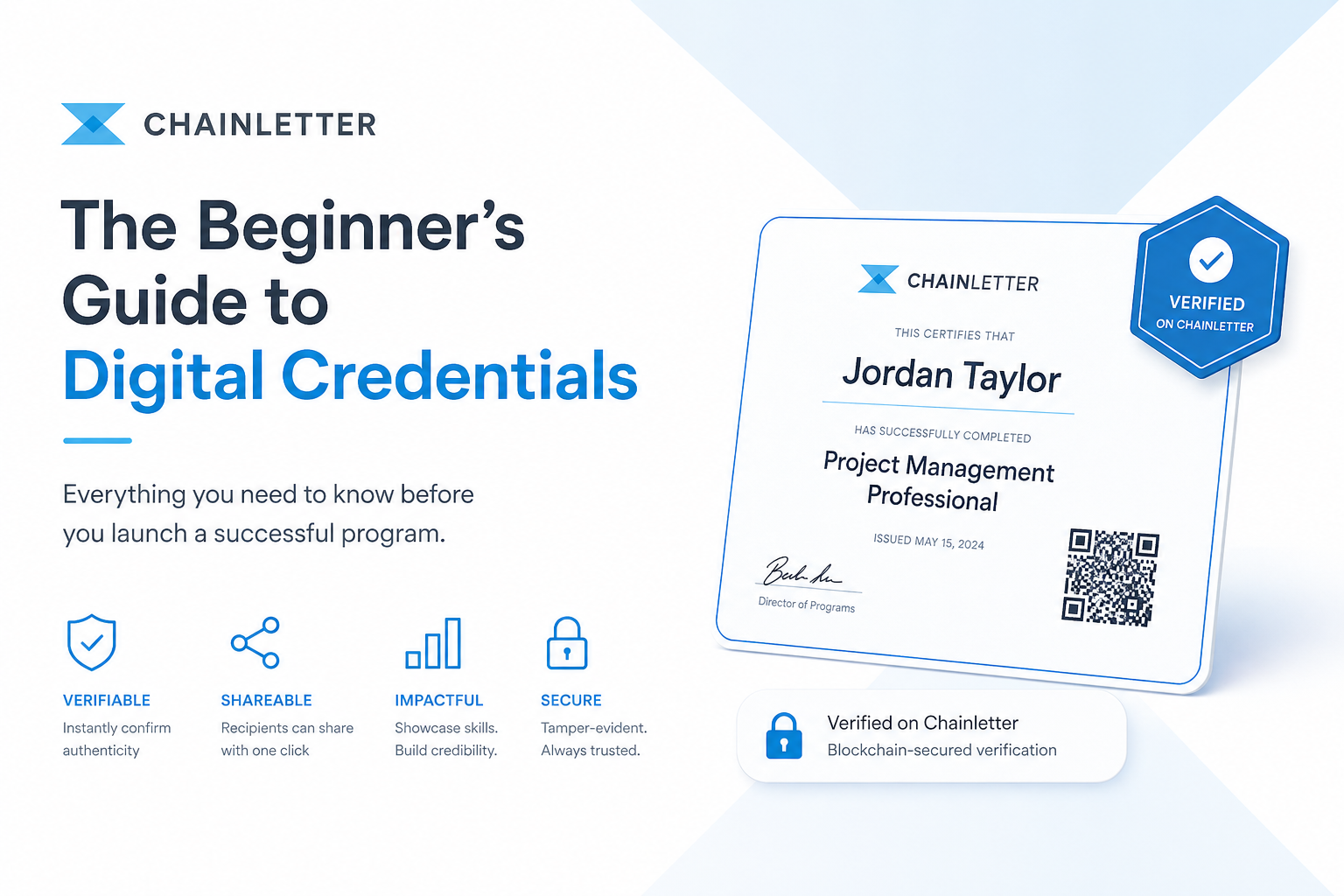
How Chainletter Approaches This Problem
Chainletter was built around a simple premise: digital credentials and documents should not require the recipient to trust a platform or contact an issuer to verify authenticity. Verification should be a permanent property of the file itself — not a service that can go offline.
Every credential or document stamped through Chainletter receives a cryptographic fingerprint that is anchored to a public blockchain. The verification record exists independently of Chainletter’s platform. If Chainletter’s servers went dark tomorrow, every file it ever stamped would still be fully verifiable — because the proof isn’t stored on Chainletter’s servers. It’s stored on a decentralized public ledger that no single party controls.
For organizations issuing invitations, credentials, or any document that needs to be trusted outside the originating system, that architecture changes what “verified” actually means. Learn more about how Chainletter works at chainletterlabs.com.
If It Matters, It Should Be Verifiable
Chainletter stamps files with a blockchain-anchored fingerprint that anyone can verify, at any time, without depending on a central system. No spoofed platforms. No broken links. No expiration date on trust.